How Your Wi-Fi Can See Through Walls
For most of us, Wi-Fi is just the invisible pipe that connects our phones and laptops to the internet. You forget it exists until it stops working.
But the radio waves your router pumps out are doing something far more interesting than moving packets. They are bouncing off every surface in your home, including you. And it turns out that by studying those bounced signals carefully, a computer can figure out where you are, what you are doing, and even who you are, all without a single camera, microphone, or sensor attached to your body.
This is not science fiction. It is a scientifically validated, peer-reviewed, and rapidly commercializing field of technology. Universities like MIT and Carnegie Mellon have published working systems. The Wi-Fi standards body (IEEE) is currently finalizing a formal specification to bake this capability into every future router. And the hardware needed to run a basic version of this attack can be bought from a hobby electronics shop for around thirty dollars.
This is a full breakdown of how it works, what it can actually do, and how you can defend against it.
Why radio waves can "see" you
Before anything else, you need to understand one key physical fact: the human body is mostly water, and water interacts strongly with radio waves.
When your router sends a Wi-Fi signal, it does not travel in one clean straight line to your phone. It radiates outward like ripples in a pond and bounces off walls, furniture, and people. By the time your phone receives the signal, it has actually received dozens of copies of the same signal, each having taken a slightly different path and arriving at a slightly different time. This is called multipath propagation.
Your router and phone handle multipath constantly because it is a basic reality of radio communication indoors. The phone's Wi-Fi chip measures exactly how each copy of the signal arrived, noting things like how loud it was and how much its timing shifted. That measurement is called Channel State Information, or CSI.
Think of CSI like a fingerprint of the room at a given moment. When the room is empty and still, the fingerprint stays basically the same. When you walk in, your body absorbs some of the signal and reflects the rest in new directions. The CSI fingerprint changes. When you breathe, your chest moves a few millimeters, and that tiny movement shifts the fingerprint slightly in a predictable, measurable way.
Wi-Fi sensing technology watches that changing fingerprint and reverse-engineers the physical event that caused the change.

How Wi-Fi signals are structured: OFDM and subcarriers
Modern Wi-Fi does not send data on one single frequency. It splits its bandwidth into dozens of smaller channels called subcarriers, all transmitting in parallel. This system is called Orthogonal Frequency-Division Multiplexing, or OFDM.
The reason this matters for sensing is that CSI is measured per subcarrier. So instead of a single number describing the channel, you get a dense table of measurements, one row per subcarrier, each recording both the amplitude (how loud the signal was) and the phase (how much its timing shifted). A typical Wi-Fi setup gives you 30 to 256 of these per measurement, updating many times per second.
That level of detail is what makes high-resolution sensing possible. A single broad measurement of signal strength would tell you almost nothing. But a full per-subcarrier CSI report, updated 100 times per second, captures tiny environmental changes with remarkable fidelity.
Imagine you are blindfolded in a room. Someone claps once. You hear the clap directly, but also hear it echoing off the walls, arriving a fraction of a second later from different directions. From those echoes alone, you could estimate the size and shape of the room. CSI works the same way, except instead of sound echoes, it is measuring radio wave echoes, and instead of room shape, it is measuring human presence and movement.
Two ways to build a sensing system
All Wi-Fi sensing setups fall into one of two camps depending on whether they send their own signals or just listen to existing ones.
Active sensing: the system does the transmitting
An active system uses a dedicated transmitter to deliberately fire Wi-Fi pulses into the environment and measure the echoes. MIT's "Wi-Vi" system is the clearest published example.
The big challenge with active through-wall radar is that the wall itself reflects the signal far more strongly than any person behind it. To solve this, Wi-Vi uses two transmit antennas. Both transmit nearly identical signals, but one is mathematically inverted. When those two signals bounce off something stationary like a wall, they cancel each other out completely. A moving human, however, reflects the signals in a slightly different way each moment, which means the cancellation is never perfect. The human's reflection leaks through the filter while the wall disappears. The system then tracks that leaking signal to estimate location and movement direction.
Passive sensing: the system just listens
A passive system does not transmit anything at all. It just sits silently and listens to Wi-Fi signals already in the air, such as the constant background chatter between your router and your smart TV.
This is the more threatening of the two approaches from a privacy standpoint. Because the sniffer device never transmits, it is completely invisible to your network. Standard security tools cannot detect it. It does not need to know your Wi-Fi password. It does not need to decrypt a single byte of your internet traffic. All it needs is the physical layer signal measurements, which are broadcast openly as a side effect of how Wi-Fi works.
The signal could be encrypted end-to-end with the strongest cipher available, and none of that would matter. The physics of wave propagation still reveals where you are in the room.
The hardware: from lab equipment to a thirty-dollar chip
Until fairly recently, extracting raw CSI data required expensive, specialized hardware and a custom-built Linux setup. The Intel Wi-Fi Link 5300 network card running modified firmware was the standard tool for years, and getting it working was a significant technical undertaking.
That barrier has largely disappeared.
| Tool | Hardware | What it can do |
|---|---|---|
| CSITool (Intel) | Intel 5300 NIC | The original research tool. Captures 30 subcarriers at basic resolution. |
| Atheros CSI Tool | Qualcomm Atheros chips | Works on many embedded Linux boards and OpenWrt routers. |
| Nexmon CSI Extractor | Broadcom chips (Raspberry Pi, many smartphones) | Captures up to 256 subcarriers on 4x4 antenna arrays. |
| ESP32 CSI Toolkits | ESP32 microcontroller (~$30) | Full CSI capture on a tiny chip. Supports onboard AI, local storage, and web dashboard. |
| ZTECSITool | ZTE Wi-Fi 6 hardware | Next-generation tool supporting the widest bandwidths and highest data resolution. |
The ESP32 entry is the one that changed the threat landscape. This is a microcontroller the size of a credit card, available at any electronics supplier, that can capture and process Wi-Fi sensing data with no laptop attached, run for hours on a battery pack, and fit inside a hollowed-out book. The gap between "sophisticated academic research" and "thing a motivated person could build at home" has closed substantially.
How AI turns radio waves into a picture of your body
Raw CSI data is just a stream of numbers. Turning it into an image of a person's body requires a trained AI system, and training that AI system requires solving an interesting problem: how do you teach a model to understand radio waves when radio waves do not look anything like the images humans are used to annotating?
The solution is called cross-modal supervision, and it uses a "teacher-student" setup.
During training, researchers run both a Wi-Fi receiver and an optical camera simultaneously in the same room. The camera feeds into an established computer vision model (the "teacher"), which already knows how to find human body joints in images and outputs precise skeletal coordinates for each video frame. The Wi-Fi receiver feeds into the new "student" model, which receives the CSI data for the exact same moments.
The student is penalized every time its output disagrees with the teacher's skeletal estimate. Over thousands of training examples, the student learns which patterns in the CSI data correspond to which body positions.
Once training is complete, the camera is removed entirely. The fully trained student model can now estimate body poses from Wi-Fi signals alone, and because Wi-Fi passes through walls but cameras do not, the model can do something the teacher never could: track people who are on the other side of a wall.

What CMU's DensePose-WiFi system achieves
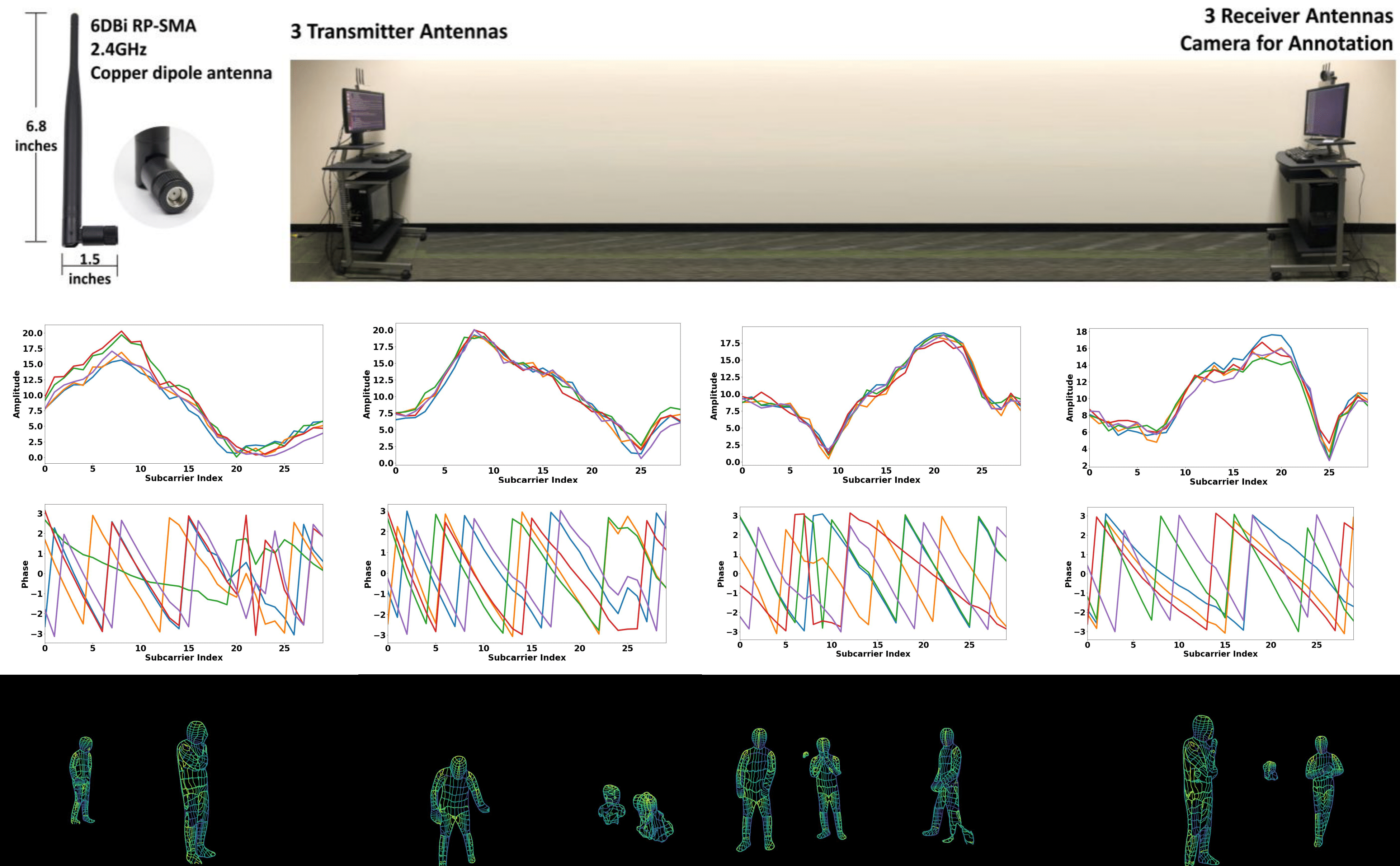
Carnegie Mellon University's DensePose-WiFi system shows how far this approach has progressed. It uses an array of three transmitters and three receivers, sampling CSI at 100 times per second across 30 subcarriers in the 2.4 GHz band.
The raw CSI phase data is inherently noisy due to antenna timing drift, so the system first runs a mathematical cleanup step to stabilize it. The cleaned amplitude and phase values are organized into large structured data tensors and passed through a neural network that translates them into a standard image-like representation. That translated representation is then processed by an architecture borrowed from computer vision (ResNet with Feature Pyramid Networks) to produce two outputs: a skeleton showing 17 body joint locations, and a dense UV map covering 24 distinct body surface regions.
In published tests, the system achieved 74% accuracy at correctly locating people in bounding boxes (and 47% at the stricter threshold requiring near-perfect box fit). For dense body surface mapping, it hit 79.5% accuracy at the looser threshold. Torso tracking is highly reliable. Fine-grained limb position estimation remains harder, but the gap is closing with each published iteration.
What the technology can actually do today
The capabilities of current systems go well beyond detecting whether someone is home.
Identifying who you are from the way you walk
Every person has a slightly different gait: the length of their stride, the way they shift their weight, the rhythm of their movement. These patterns show up in the RF skeleton the sensing system builds, and they are distinctive enough to identify individuals.
MIT's RF-Pose system tested this directly. Given just two seconds of RF skeleton data (50 frames), a classifier correctly identified the right person out of a lineup of 100 individuals with 83.4% accuracy when the person was visible, and 84.4% accuracy when they were behind a wall. The wall actually improved identification slightly, possibly because it removed visual noise. Top-3 accuracy exceeded 96% in both conditions.
A 2025 paper called "WhoFi" extended these findings, demonstrating that consistent re-identification based on RF biometrics works reliably across sessions, effectively turning any Wi-Fi network into a persistent, device-free biometric tracking grid.
Measuring your breathing and heart rate from another room
At 5 GHz, a Wi-Fi wavelength is about 6 centimeters. That is sensitive enough to detect the millimeter-scale movement of your chest as you breathe.
By applying signal processing filters to isolate the rhythmic component of the CSI variation, systems can extract clean respiratory signals from noisy radio data. Open-source platforms built on ESP32 microcontrollers achieve a mean error of just 2.7 breaths per minute compared to medical reference devices. The same approach can detect heart rate from a person sitting still or sleeping.
This is being actively marketed as a non-contact health monitoring tool for elderly care and sleep tracking. It is also, from a different angle, a way to confirm that someone is alive and approximately where in a building they are, without any cooperation from the target.
Reading text written on paper through a wall
The University of California, Santa Barbara pushed beyond human tracking entirely. Using a technique based on how Wi-Fi waves interact with the sharp edges of solid objects, their researchers demonstrated Wi-Fi imaging of stationary inanimate objects. The result was clear enough to image individual letters of the alphabet through a wall.
This is not yet a practical surveillance tool for text reading, but it establishes that Wi-Fi sensing is not fundamentally limited to tracking motion. It is evolving toward full volumetric structural imaging of enclosed spaces.
The threat in practice: the "Et Tu Alexa?" attack
The most directly actionable threat from all this research was documented by security researchers at the University of Chicago and UC Santa Barbara, in a paper titled "Et Tu Alexa? When Commodity WiFi Devices Turn into Adversarial Motion Sensors."
Here is the setup. Your home contains several smart devices, such as an Amazon Echo, a smart TV, and a few IoT sensors. These devices are always on and constantly send small packets of data to the internet to stay connected and synchronized. Every one of these transmissions fills your home with radio waves.
An attacker parks outside your building, or stands in the hallway of your apartment complex. They carry a single passive sniffer, which could be a cheap smartphone or an ESP32 microcontroller in a jacket pocket. The sniffer does not connect to your network. It does not need your password. It simply listens to the RF signal from each of your internal IoT devices as those devices transmit their routine packets.
When you move inside your home, your body disturbs the radio waves traveling between your internal devices and the outside world. The sniffer measures a statistical metric called CSI variance, which tracks how much the signal is fluctuating over short time windows. High variance on a particular device's signal means someone is moving near that device.
By watching which devices are showing high variance at any given moment, the attacker can map which room you are in and track your movement between rooms, all in real time, all from outside the building.
In testing across 11 different residential apartments and offices, this attack detected human presence with 99.7% accuracy when four internal IoT devices were active. The attack remained effective even when the IoT devices were transmitting at extremely low rates, losing only about 1.5% accuracy when devices sent just two packets per second. Large pets produced some false positives; otherwise the system was robust.
Your Wi-Fi encryption does not matter here at all. WPA3, VPNs, end-to-end encryption: none of it touches the physical layer. The sniffer never decodes a single bit of your actual data. It only watches how the physical radio signal fluctuates. Those fluctuations are a side effect of how Wi-Fi physics works, and no software update to your router will change the underlying physics.
The nosy neighbor variant
A study from Leipzig University showed a related but different angle. A researcher with a cheap Raspberry Pi and basic antennas, placed in a neighboring apartment, passively sniffed encrypted Wi-Fi and Bluetooth Low Energy signals through a shared wall.
Rather than tracking human movement directly, this study focused on classifying devices: which smart plugs, lights, and sensors were active at which times, based entirely on how frequently packets were sent and how large they were. Over days of monitoring, the system built a detailed map of the household's daily routines, identifying when people woke up, when they watched TV, when the robot vacuum ran, and when they went to bed.
No packet contents were ever decrypted. The timing and size patterns alone were enough.
The standard that will put this in every router: IEEE 802.11bf
Academic research papers are one thing. The technology becoming a built-in feature of every consumer router is another level entirely.
That second thing is happening. The IEEE, the body that writes the technical standards Wi-Fi is built on, is in the final stages of publishing IEEE 802.11bf, a formal amendment that makes "Joint Communication and Sensing" an official part of the Wi-Fi specification.
802.11bf standardizes a five-step procedure for performing Wi-Fi sensing sessions between devices:
- Session Setup: the sensing initiator contacts responders, exchanges capability information, and assigns identifiers.
- Measurement Setup: devices agree on what to measure and how to report results.
- Active Measurement: real-time channel measurements are taken, extracting Angle of Arrival, Time of Flight, and Doppler frequency shift for objects in the environment.
- Termination: resources are released cleanly.
- Device-Free Sensing: the explicit design philosophy is that targets do not need to carry any hardware.
For the 60 GHz frequency band (millimeter-wave), the standard enables ultra-high-resolution spatial data because the short wavelengths are far more sensitive to fine detail.
The market implications are significant. When sensing is baked into the protocol standard, chipmakers include it in every new Wi-Fi chip. Device manufacturers enable it in firmware. ISPs like Comcast and Plume have already quietly rolled out basic motion detection features to millions of residential gateways, marketed as "Home Awareness" and "Smart Monitoring." 802.11bf will make that universal and interoperable across brands.
Published accuracy benchmarks for 802.11bf-compliant systems show 92 to 97% accuracy for human presence detection and 88 to 94% accuracy for activity classification, at 40 to 65% lower deployment cost than equivalent camera networks.
The privacy companion standards
The IEEE is not completely ignoring the privacy implications. Two parallel efforts address some of the concerns:
IEEE 802.11bh standardizes the use of Randomized and Changing MAC (RCM) addresses. Your device's MAC address is a hardware identifier that stays the same across sessions by default, making it easy to track a device as it appears on different networks. MAC randomization makes that identifier change periodically so trackers cannot follow a device over time. This is a meaningful protection against digital identity tracking. It does not, however, prevent someone from using your device's radio emissions as a radar illuminator. The physical signal still exists; only the software label on it has been obscured.
IEEE 802.11bi addresses broader data privacy within the protocol, aiming to reduce risks from eavesdropping and identity inference.
Both amendments are useful. Neither addresses the root problem, which is that the physics of wave propagation means human bodies will always interact with radio waves, and there is no software patch for physics.
Physical countermeasures: blocking the signal at the source
Because passive sensing attacks leave no trace on your network and cannot be detected by conventional security tools, the most reliable defenses are physical.
The goal is to prevent Wi-Fi signals from crossing your building's walls in a way that is useful to an outside sniffer.
Building a Faraday cage around your space
A Faraday cage is an enclosure made of conductive material that blocks electromagnetic fields from passing through. The key rule is that the gaps in the conductive mesh must be smaller than one-tenth of the wavelength of the signal you want to block.
For 2.4 GHz Wi-Fi (wavelength around 12.5 cm), the mesh holes must be smaller than 1.25 cm. For 5 GHz Wi-Fi (wavelength around 6 cm), holes must be smaller than 0.6 cm.
Standard chicken wire is not tight enough to provide real protection for imaging purposes, though it will degrade signal quality. A proper Faraday enclosure requires a fine metallic mesh meeting those specs.

Practical retrofit materials for existing buildings
| Material | Product Examples | How it works |
|---|---|---|
| EMI Paint | MWT Materials ME-565 (water-based), ME-505 (solvent-based) | Paint containing conductive copper, silver, or nickel particles. Applied like regular paint, creates a continuous conductive layer on walls. Standard in government SCIFs. |
| Conductive Wallpaper | EMShield, MWT ME-2100 | Same principle as EMI paint in sheet form. Less obvious in appearance, useful in corporate environments. |
| RF-Blocking Window Film | Signals Defense DAS Shield, Guardian Bastille | A microscopic metallic layer in the film reflects 2.4/5 GHz signals. Installed like tinted window film, maintains optical transparency. |
| Architectural Mesh | Aluminum or copper mesh embedded in plaster or drywall | Must meet the 1/10th wavelength rule to be effective (holes smaller than 0.6 cm for 5 GHz). |
Standard glass is nearly transparent to Wi-Fi. EMI paint on your walls does almost nothing if your windows are unprotected. RF-blocking window film is essential for any serious shielding implementation, and even Low-E glass (common in modern double-pane windows) provides only partial natural attenuation.
Software countermeasures: fighting back at the router level
Physical shielding requires significant cost and effort. For most people, software-level defenses are more realistic. They are not as definitive as a proper Faraday enclosure, but they can substantially degrade the quality of a sensing attack.
AP-based signal obfuscation
This defense was proposed directly in response to the "Et Tu Alexa?" attack. The idea is to make your access point actively sabotage an outside sniffer's measurements.
Two techniques work together:
Power randomization: the router randomly varies its transmission power over time within a defined range (for example, fluctuating by up to 10 dB). This creates artificial signal variance that drowns out the natural variance caused by human movement. The attacker cannot tell the difference between "person walking" and "router randomly changed power."
Cover traffic injection: the router deliberately sends fake packets timed to look like they came from your internal IoT devices. Because the attacker's analysis relies on isolating specific devices and measuring their signal variance, flooding the analysis window with additional fake traffic breaks the isolation step.
In university trials, this combined defense dropped attack detection rate from 99.7% down to 47.48%, while pushing the false positive rate up to nearly 50%. At that point the attack is essentially useless because it cannot reliably distinguish between motion and noise.
CSI scrambling and the AntiSense approach
A more sophisticated approach targets the CSI data itself at the physical layer. The AntiSense protocol does not jam the Wi-Fi spectrum (which would break everyone's internet). Instead, it uses an active device to superimpose a precisely engineered signal on top of legitimate transmissions. This superimposed signal is calculated to scramble the spatial and Doppler features of the CSI (the exact features needed for localization and pose estimation) without corrupting the data payload that carries actual internet traffic.
Early implementations demonstrate that AntiSense can effectively blind both passive sniffers and active multi-antenna sensing systems while maintaining normal communication performance.
Open-source projects like the OpenWiFi CSI Fuzzer take a related approach, injecting synthetic or corrupted multipath data into the CSI feedback loop so that any system reading the CSI gets a distorted picture of the room's geometry.
Router configuration steps you can take today
Consumer routers in 2026 generally do not include a "CSI obfuscation" toggle, but there are practical steps that meaningfully reduce your exposure:
Disable ISP-provided sensing features. If your router has settings labeled "Home Awareness," "Smart Monitoring," or "Wi-Fi Motion Detection," turn them off. These features intentionally use sensing capabilities and their data may be processed on the ISP's servers.
Use open-source firmware. OpenWrt or DD-WRT gives you granular control over your router's Linux kernel and wireless drivers. One of the most useful options is manually lowering your router's transmit power. The lower the power, the shorter the range at which a passive sniffer outside can get a clean signal.
Prune your IoT devices. Every smart device in your home is a potential radar illuminator for an outside sniffer. The more devices, the more angles of coverage, the higher the sensing accuracy. Removing IoT devices you do not genuinely need directly degrades the quality of a potential passive attack.
Enable wireless client isolation. This setting prevents your devices from talking to each other directly across the local network. It does not stop physical-layer sniffing, but it limits the ability of a compromised device to map your network topology or relay information to an attacker.
Choose privacy-focused hardware. Vendors like GL.iNet build routers with MAC randomization, randomized broadcast identifiers, and strict DNS encryption as defaults. These reduce digital fingerprinting and side-channel data leaks.
Detecting intrusions: auditing your network
Because passive CSI sniffing leaves zero trace on your network, detecting an outside passive attacker is not currently possible with standard tools. What you can do is detect active anomalies: rogue access points, unknown devices on your network acting as unauthorized anchors, or evil twin networks designed to intercept your traffic.
| Tool | Type | What it helps with |
|---|---|---|
| Fing | App (desktop and mobile) | Scans your local network and identifies every connected device. Catches unknown devices that could be acting as unauthorized sensing anchors. |
| NetSpot | PC/Mac app | Generates Wi-Fi heat maps and reveals unknown SSIDs broadcasting nearby. Useful for spotting rogue access points. |
| SolarWinds NPM | Enterprise software | Tracks network paths and anomalous signal behavior at scale. Identifies active rogue APs and unusual traffic patterns. |
| PRTG Network Monitor | Enterprise software | Automatically detects new devices and flags unusual MAC addresses or traffic bursts. |
| Latnex SPA-6G | Spectrum analyzer (hardware) | Provides a visual display of all wireless activity up to 6 GHz. Identifies persistent unauthorized transmissions in your vicinity. |
| LawMate RD-30 / iProtect RF Detector | RF wand (hardware) | Sweeps a physical space for hidden transmitters, GPS trackers, and malicious IoT devices. |
For high-security environments, professional TSCM (Technical Surveillance Counter-Measures) equipment and specialists are the appropriate tool. A spectrum analyzer will show you every transmitter in a space. An RF wand will help you locate them physically.
The legal landscape: law has not caught up
The technology is moving faster than the laws meant to govern it, and the gaps are significant.
United States
In the US, intercepting Wi-Fi signals intersects with the Wiretap Act. A federal ruling in the case of In re Innovatio Ventures created a significant gap: the court found that capturing unencrypted Wi-Fi data packets using commercially available sniffers costing under $700 does not violate the Wiretap Act, on the grounds that signals broadcast over unsecured networks are "readily accessible to the general public."
This creates a direct legal loophole. Passive CSI sniffing for motion detection and surveillance is arguably entirely legal for civilian actors under current US federal law.
On the constitutional side, the Fourth Amendment protects against unreasonable government searches. The Supreme Court's landmark ruling in Carpenter v. United States established that the government needs a warrant to access persistent historical location tracking data, recognizing that digital technology enables a form of near-perfect surveillance that violates reasonable privacy expectations.
However, the application of that Carpenter logic to real-time through-wall Wi-Fi radar has not been directly tested at the Supreme Court. The Court recently declined to hear Moore v. United States, which challenged warrantless use of pole cameras for continuous exterior surveillance of a home. That refusal leaves the circuit courts divided, and law enforcement use of Wi-Fi radar to see through walls remains in legally ambiguous territory.
Meanwhile, state attorneys general are beginning to take action against uninvited data collection by smart devices. Texas AG Ken Paxton filed a lawsuit against five major TV manufacturers (Sony, Samsung, LG, Hisense, and TCL) for using Automated Content Recognition to secretly record viewing habits. While that case involves screen data rather than RF sensing, it reflects a growing legal intolerance for invisible data harvesting inside the home.
European Union
The EU approach is substantially stricter. Under the GDPR, "personal data" is defined broadly. If CSI data is processed to generate biometric signatures, track movement patterns, or identify individuals by their gait (which MIT's RF-Pose and WhoFi demonstrably do), it definitively qualifies as sensitive personal data requiring explicit informed consent before collection.
Any EU company or ISP deploying Wi-Fi sensing without affirmative user consent is in violation of the GDPR. MIT's CSAIL team acknowledged this in their RF-Pose research, outlining plans for a physical consent mechanism where a user performs a specific gesture sequence in front of the router to opt in to monitoring.
The contrast with US law is stark. EU rules are proactive and rights-based. US rules are largely reactive, requiring demonstrated harm before legal protections apply. For an attack that leaves no evidence and whose harm is often invisible, that distinction matters enormously.
What this all means
The technology is real. The physics is settled. A Wi-Fi signal bouncing off a human body carries enough information about that person to detect them, track them across rooms, estimate their body pose, measure their breathing and heart rate, and identify who they are with high accuracy, all from outside the building, with no cooperation or awareness from the target.
The tools needed to do this are not classified or expensive. They are available on Amazon.
The IEEE is standardizing this capability into every future router.
The laws in most jurisdictions have not caught up.
None of this means the situation is hopeless. Physical RF shielding works. Active signal obfuscation at the router level degrades attack accuracy substantially. Reducing the number of IoT devices in your home directly reduces sensing resolution. And legal frameworks are, slowly, beginning to recognize that physical layer metadata like CSI is sensitive biometric information that deserves protection.
The realistic near-term response is this: treat your Wi-Fi signal as something that leaks information about your physical presence, because it does. Apply the same thinking you would to cameras: consider what can be seen from outside, limit unnecessary exposure, and push for regulations that treat RF biometric data with the same seriousness as any other form of biometric surveillance.
The eye is already open. The question now is whether we choose to look back at it.
If this was worth sharing, send it to someone on 𝕏 or LinkedIn. Got a question or a thought? Drop me a message , I read everything. If this was worth your time, .